
After five months of development, a new version of Tor Browser 9.0 has been released, which is focused on ensuring anonymity, security and privacy. All traffic to the Tor browser is sent only through the Tor network and it is impossible to access directly through the regular network connection of the current system, which does not allow to trace the real IP of the user.
To provide additional protection, the package includes the HTTPS Everywhere plug-in, which allows traffic encryption to be used on all sites whenever possible. To reduce the threat of JavaScript attacks and block plugins by default, the NoScript plugin is included. To combat traffic blocking and inspection, fteproxy and obfs4proxy are used.
Main new features of Tor 9.0
In this new version of the browser it was migrated to the new significant version of Tor 0.4.1 and the ESR branch of Firefox 68.
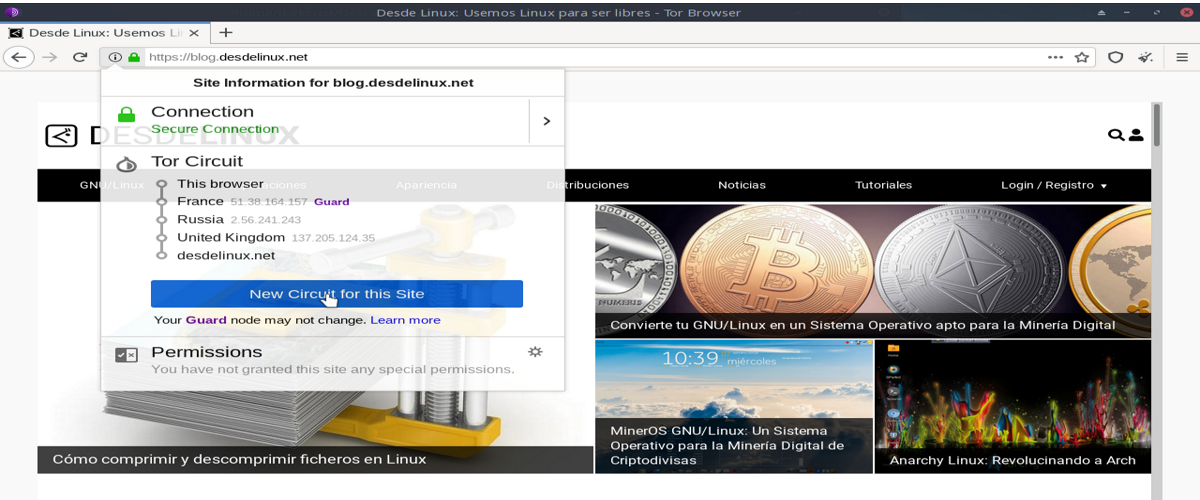
In the browser interface removed the "Onion" button from the panel. The functions of viewing the route of traffic through the Tor network and requesting a new chain of nodes used to forward traffic to Tor are now available via the "(i)" button at the beginning of the address bar.
The «New Identity» button has been moved to the panel, Through which you can quickly reset the settings that sites can use to covertly identify the user (changing the IP by setting a new string, clearing the contents of the cache and internal storage, closing all tabs and windows). A link to change identities is also added to the main menu, along with a link to request a new chain of nodes.
In Tor 9.0 we can also find the inclusion of the technique ID lock Letterboxing. This add indents on each tab between the window frame and the content displayed to avoid being adjusted to the size of the viewable area. The indentation is added with the calculation of bringing the resolution to a multiple of 128 and 100 pixels horizontally and vertically.
In case the user resizes the window, the size of the visible area becomes a sufficient factor to identify different tabs in a browser window.
Torbutton and Tor Launcher plugins are integrated directly into the browser and they are no longer displayed on the about: addons page. Tor specific connection settings via bridge nodes and proxies were carried over to standard browser settings (about: preferences # tor).
Even when it is necessary to bypass censorship where Tor is blocked, through the regular configurator, you can request a list of nodes bridge or specify bridge nodes manually.
By choosing the "safest" security levels asm.js is now disabled by default. Added support for “meek_lite” -based bridge nodes, simplifying connection to Tor in countries with strict censorship (forwarding through Microsoft Azure cloud platform is used).
While for the Android version browser support was added for Android 10 and the ability to create x86_64 versions for Android (previously only the ARM architecture was supported).
If you want to know more about the details of this new Tor release, you can consult them In the following link.
How to install Tor 9.0 on Linux?
For those who are interested in being able to install this new version of the browser on their systems, they can do so by following the instructions that we share below.
For those who are Arch Linux users, as well as derivatives of it, such as Manjaro, Arco Linux, among others. The installation can be done directly from the AUR repositories and with the help of an AUR assistant.
From a terminal we just have to type the following command:
yay -S tor-browser
For the rest of the distributions of the distributions from Linux, they will have to download the browser package from the link below.
Once the download is done, we can unzip the package from the terminal with:
tar Jxvf tor-browser-linux64-9.0_en-US.tar.xz
We enter the resulting directory with:
cd tor-browser_en-US
And we run the browser with:
./start-tor-browser.desktop