Again, video game researchers discovered an "innovative" phishing technique (spoofing) that does a very good job of masking the scammers' intentions.
As one of the world's largest digital distribution platforms for video games, Steam features a variety of community UX elements, such as friend lists and the ability to exchange game items with other users.
While this strong focus on the community has helped Steam stand out in an increasingly crowded market, it also leaves users open to deceptive practices.
The need for surveillance on the platform was again alerted during the weekend, when A 22-year-old computer science student by the name 'Aurum' provided details of a new phishing scam for Steam.
A website to steal Steam accounts
According to the researcher, the phishing site not only tried to fool users with a valid SSL certificate, but also a small piece of JavaScript which would generate a pop-up window stating that the server was heavily loaded and asking the victim to log in with their Steam account. for access to the site.
In Aurum's words he describes how he realized it:
“The chat seemed straightforward, the scammer wanted to give me an obviously profitable trade (they kept trying to get me to add them to Discord for some reason).
Near the end of the “trade” discussion, I was asked to log onto a convenient Steam pricing website so they could get an idea of how much my stuff was worth.
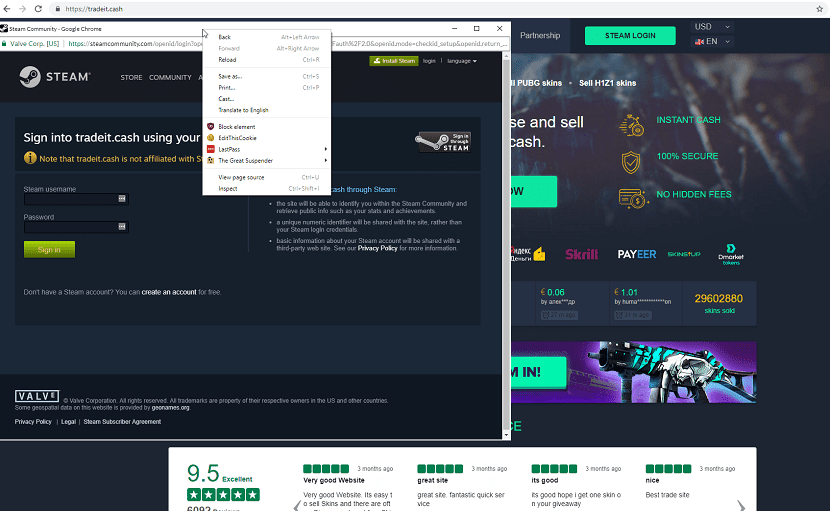
The phishing site, https://tradeit.cash. The website was essentially a copy of a legitimate Steam website, https://skins.cash. "
Although scammers created a legitimate looking popup, Aurum found that it did not result in two instances of Chrome on the taskbar, and that it was "just one window within the phishing website."
"They had even made some buttons for the Chrome UI elements," he said. "This was confirmed by trying to right-click in the title bar area of the pop-up window, which opened the right-click context menu of a web page."
Hackers took the time and "hassle" to host their phishing site on CloudFare and even choose to use a CloudFare SSL certificate to make it as reliable as possible.
The phishing started with a pop-up that asked you to enter Steam, claiming that the "phishing" site was overloaded.
About the fake website
The Steam Phishing Site used a picture-in-picture phishing technique to simulate an OpenID login screen without failures.
Aurum sensed that something was wrong, as the site that he believed to be fake from the beginning was opening an OpenID Steam login pop-up.
Attacks of this nature are certainly nothing new. A similar technique has been described in this document since 2007.
Steam already includes a detailed guide aimed at helping users keep their accounts safe.
The site is currently offline because the DNS record was removed about a few hours ago.
However a user got a snapshot of the site and all code before it was removed, and took the liberty of sharing it on GitHub. The link is this.
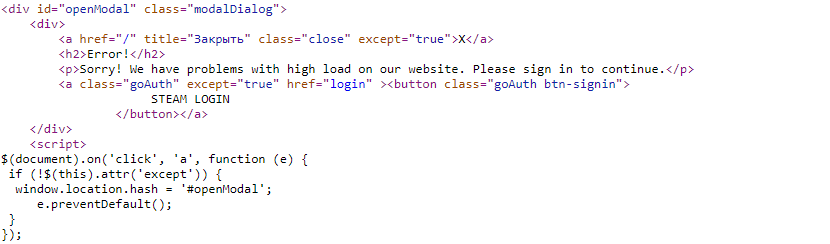
It's pretty simple code, in the end.
The hackers copied the legitimate trading site as well as the Steam Community login page, then added JavaScript code to both, as well as tweaking the HTML a bit.
In total, three JS snippets were added: the first one detects debuggers (the bit that found the original blog poster), the second opens the fake browser and pastes the fake login page inside an iframe, and the third (which runs on the iframe) collects the credentials from the page from Steam login copied.
As my grandmother used to say, beauty is in simplicity. Simple, effective and beautiful, a piece of code.
I read the full article ... And what is it related to linux?