Finally, we can say that we have significant enough market share for malware makers to pay attention to us. Only in this case it is not malware for Android, but malware for Linux distributions for the desktop.
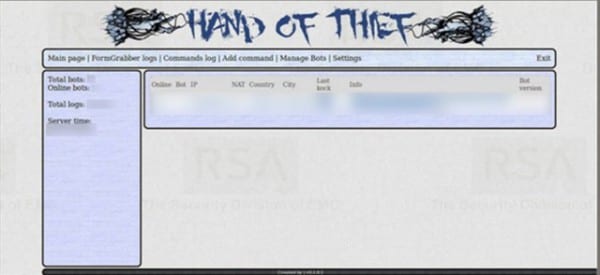
Hand of Thief is a banking Trojan developed in Russia that was successfully tested on 15 distributions including Ubuntu, Debian and Fedora and on 8 desktop environments (GNOME and KDE included obviously) and can be sneaked into any browser (including Firefox and Chrome)
And what evils does he do? A banking Trojan is like a keylogger designed to detect string patterns. Steal cookies, collect computer and browsing data even using HTTPS, and block infected machines from accessing sites that offer security updates. What is not clear is how it manages to infect its victims (they speak of links and form grabbing, but a specific path or vulnerability is not specified).
It is also mentioned that malware can be sold (as if it were software for everyday use) in certain underground forums for 2000 dollars, a fairly high price compared to the price paid for malware for Windows, but reasonable considering the ease of compromising Windows .
Sources:
http://muyseguridad.net/2013/08/09/hand-of-thief-troyano-bancario-linux/
I was just reading the news in the source and the only thing that generated me was a smile.
I would not pay 2,000 dollars for a malware that in the end has to be installed by the user with his password to work 🙂
And on top of that, you can see it running when you run the TOP process viewer.
I have to be careful with AUR
The good thing about Linux is that its users are usually more aware of the implications of installing external software. Those who use Linux in an amateur way or they read or believe that without caution something can happen to them (as cabj says about AUR).
I think that the truth is that they are paying us so much attention and on the other hand it is very difficult to do in Linux that someone pays 2,000 dollars just for a little information, I do not think it will be very commercial, but you always have to beware.
I suppose that if I do not commit the idiocy of falling into social engineering tricks, I have installed a Firewall and I am careful with what I install from AUR / Launchpad I do not have to worry, right?
I do not think so.
@Diazepan smells like a yellow note lol I don't like it, even if you don't have a firewall or antivirus (I've never installed one for linux) and the permissions system ??? if in windows and mac it asks every time something tries to enter the system and save something, why should it enter linux which is less permissive ??? for me that are lies uu
The note is yellowish for others, because as it is well known in GNU / Linux, unless you spend very lightly installing software from sites or repositories of dubious origin, there is no possibility that this will affect you, and the reason is Very simply, the "Trojan virus" cannot infect the machine unless you give it the sudo password (insert laugh here).
Let's not let anyone with some prudence and intelligence install a program that will do miracles with your Linux or that promises to make you rich overnight, since as the same "sales advisor" of the Trojan says: "I suggest the use of email and social engineering as an infection vector. » so @gato, yes, you are absolutely right with your comment.
I say that, the only antivirus is the user, it depends on the factory if it is good or bad (a verse xD).
I guess it's one of those Russian scams.
Most turn out bad.
Don't worry, most AUR programs are supervised by other users, just take a look at the PKGBUILD download URL.
Well, the truth is that Linux is gaining more and more market, and 2000 dollars is actually quite low considering that most servers in the world are Linux, if someone has access to the information contained in them, it can cause quite significant damage such as for example the banking area ... but as always happens later, the entire community has to resolve this issue ... xD
I don't know, but that just smells like rumors to me xD, I still don't understand how it infected me, I don't understand it, I already read almost all the blogs that talk about the Trojan but its operation is not clear to me, a window will pop up telling me to enter your root password to be able to steal your data? Will it kill the firewalld, will it leave me unable to use any of the tty? , and as I read in the comments of the note in English where it was published, they were saying that it is very difficult for GNU users to fall into these types of attacks, the truth is that they have another culture of Internet browsing if you can call it that , the absent-minded is not lacking 😛
For now, what is known about this "Trojan" is that it is nothing more and nothing less than a keylogger with a backdoor.
Have and where do you get the software, how does it bypass the root password, the firewall, and how does it disable security updates, does it delete sources.list or what? nobody says how it works, they are crazy. If it does all that minimum, it would have to know how to violate the root.
True. Also, I have seen quite a few programs that use SUDO to be able to install dependencies (even Steam uses it), making the system a little more vulnerable and therefore I prefer to use root over sudo.
If it breaches root and daemons the kernel, then use BSD. For now, I did not see any relevant vulnerabilities that make you distrust that system.
How does a virus affect Linux, if it does not have our root, how would it affect the kernel and the different daemons in services that are always running the system ... I had time with Linux and never had problems in that sense. The most that can happen is that it affects the system itself with some configuration ...
you are right the user is the biggest weakness not only of linux but of any operating system.
If not, look that almost 5 years ago I ignorantly executed this command in / home and /:
dd if = / dev / zero of = / dev / hdd bs = 8192
You can imagine what happened next.
And if you don't password root it anyway, it would generate a passkey to proceed with sensitive functions like daemons.
mmmm but viruses have already appeared for linux, but trojans have not noticed me.
puff I don't remember what year it was 2009-2012 I don't remember what year it was, that 50 viruses were released for Linux and it took about 7 months to resolve and install all the necessary patches.
Today in 2013 I see something new thanks desdelinux, I almost thought that Linux was indestructible.
regards
PS: It would be an oṕcion that you will talk a little about FREE BSD to see the opinion of the experts.
If you have swung with that one. There were no viruses for linux in those years. And I doubt that more than 10 have been made in all of history. In addition, here we talk about Trojans, its programming is not more complex and does not depend on system failures, it is just one more application with functionalities that the user is unaware of.
In that I agree with you.
Friend, Posix systems do not support viruses. A virus, by definition, is SELF-REPELLENT, and that's just out of context on posix systems.
Malware all you want, because there it depends on the clumsiness and idiocy of the user.
+1 man, these types of notes are nothing more than tabloid at their finest.
50 Linux viruses and they took 7 months to patch? LOL!
Are you sure you use Linux or Windows?
In my life I have heard viruses for Linux and I hope I do not hear it 😀
If that malware requires SUDO to access, then I'm safe [Ok, no].
Well, I hope that among all the known distros they make their respective reviews to release their updates as soon as possible and thus avoid finding exploits.
I was amused by this news when I saw it on the cover, for the simple fact that a few months ago I was testing the clamtk antivirus. When performing a recursive scan of the .mozilla directory, my surprise was that my browser was infected with malware such as "phishing" and something related to "bank".
For this reason, reading this news has been funny to me, for that reason I invite you to analyze your team out of curiosity.
Phishing generally does not work like this, since its main objective is to make the victim provide the desired information himself. The result that clamtk threw you could be because in your temps there was some script code of some phishing that runs on the internet, which are many, but fighting this evil is very simple, every time you enter your bank page or some private service , clean your temporary and problem solved.
Tools like HTTPS Everywhere, WOT and NoScript will make your system more secure against this type of thing, another thing that helps and a lot is simply to verify that the addresses of the web pages you visit before providing information.
The most tangible tool for these cases is to enter unknown websites in hidden mode (incognito in Chrome, private tab in Opera and Firefox / Iceweasel). That practically worked for my brother and they never robbed him again.
Well yes, Incognito mode has been a great tool in terms of security in this matter.
They found out what happened with lavabit.com, enter the site and see. I went to read my mail, and chann… Is it because of the Edward Snowden case?
Lavabit, the mail service used by Snowden, closes
Yes, here is an alternative that is paid but that offers the same and is based in Switzerland
https://mykolab.com/
Good option, although to my bad luck (rather, my bad choice), more than 8 years ago I sacrificed my privacy.
This is getting a lot of hype about this and it's just a show that fucks you up, like any other. The difference is that this one wants to hurt you.
The one who does not get it is that he believes that programs are created by themselves.
There will always be someone who installs something that does not know its reference.
Now with AUR, Launchpad and the like, well, you always have to be careful (and it's easy to know that the AUR package is going to be installed for you), also surely that in no time Mozilla and the Chromium people close the security hole, especially the second, that paying Google $ 2.000 is small change XD
For them it is convenient to investor that US $ 2000 in giving it to the first cracker who finds the Achilles heel of their browser (Chromium / Chrome) and incidentally, of the GNU / Linux kernel.
I think it is difficult that one day we will see Linux as full of malware as Windows, but the snowball has started to run ... although a little slow.
We must always be careful when using our equipment, it does not matter if we have Linux, Windows, OSX, etc.
Obviously, since it is protected with user permissions, and the truth is that it is quite common to put these failed virus attempts.
Furthermore, the Linux kernel is a benchmark in quality when compared to the BSD kernel.
I just made a request to Linus Torvalds from his Google+ if he can correct this vulnerability in the new Linux kernel 3.11 to see if he can so that we can live without the hand of the thief stalking us closely 🙂
At least Linus must be crashing with laughter with that comment 😀
I don't know if this is the first really working virus for Linux or is it the most convincing internet scam that has been created in recent years.
I argue that it is a scam, a very far-fetched one indeed.
That must be. Let's see if they can figure it out.
Malware for UNIX-based systems has been around for a long time. Be it backdoors, rootkits or keyloggers. But one generally installs them after compromising the system.
Salu2
Well, as they say, the weakest part in the security of the operating system is the user.
According to Angel Le Blanc.
pucha, it leaves me thinking and maybe the bad times will come
Don't worry, In GNU / Linux, viruses practically don't work because of the permissions system that is in the system.
Malware on GNU / Linux?
HAHAHA
Well, I think that everything also depends on the user and the precautions they have, if one remains alert there is no need to worry