It has happened to me on numerous occasions that I am working on a terminal of my laptop and at that precise moment they request me in another office, or I have 'something' doing in a terminal and for convenience or necessity I must let a friend of mine use it for a few minutes my laptop, in cases like this ... How do I protect what I do in the terminal without having to completely block the user session?
Fortunately the package exists: vlock
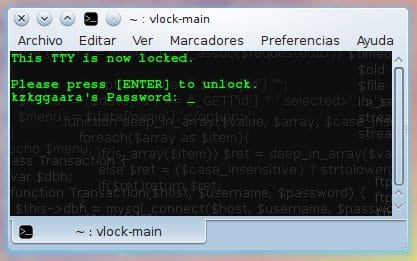
Install this package on your system and then just run it in a terminal (vlock), they will see that the terminal was blocked / protected and until they press [Enter] and enter the password, this will continue 😉
If you want to see the log referring to failed attempts, successful login attempts and more, you just have to do a cat to the /var/log/auth.log file passing it as a parameter to grep "Vlock"
That is:
cat /var/log/auth.log | grep "vlock"
This is a simple tip yes, but it has already been useful to me ... I hope you too 😀
regards
The +1 program is very interesting, although I do not find it as useful in a situation as the one you mention, because to be able to execute important commands you need the root pass and if they have that pass you are up to your hands xq with ctrl + alt + f1 or f2 etc they open a tty and log in as root and do the same damage.
In addition, the commands that can be accessed from the terminal as a normal user, in a large number of cases, they can be accessed via programs. In addition to the fact that Read, copy, delete files, and you can even put in the autostart a link to a spy program hidden inside the $ home and that would open every time you start the session, among many things.
It seems to me that the program is more than anything thought out, for when several pcs are administered and the users who use them do not want to be able to access a terminal added to the reduction in the number of tty terminals, unless this program also blocks them .
I agree with you. That does not prevent another terminal from opening. And if you want to see what the other was executing before then I see the file ~ / .bash_history (or similar depending on the distro)
Although it is an interesting package I think it is best to block the session.
It seems useful, although I still see better to lock the session ... if what you have is fear of losing your bash session I recommend using GNU screen. If you access it with the arguments "screen -D -R" you will always access the same session, exit it with the keyboard shortcut "Ctrl + a" and "d" (that is, first you do Ctrl + a and then you press "d »), So you tell the program to keep the session open in the background.
Thanks for the tip!
PS: this is only for the user who tries to use our terminal in our logged session, right? .. It could also be possible to block the shell when creating a user or modifying the existing!
Even so, you are appreciated!
Regards!
Let's see, it is assumed that to open another terminal you must enter a username and password.
Different is that we are under a graphical environment and we execute xterm or any other.
I would bet more on an application that blocks the entire computer, including the X.
I disconnect the keyboard and take it with me 😛
It can be useful when one does not use the graphical environment and is in the tty playing chess or tweeting, then they do not interfere with you and you continue with yours.
You can't Alejandro, I remember when the green phosphor monitors existed and they were insufferable, they melted your eyes, that's why later they changed them to amber and later to monochromatic.
And on top of that you add that background full of letters, you're wrong! Hahaha !!! 😀
As for vlock, notice that there is a nice fork called vlock-matrix that obviously shows you the cascade of letters when it locks the screen.
This cascade can be configured according to the characters you want to appear, the color, etc. The only downside it has and why I don't use it is that it seems that the "matrix" effect consumes too much processor for my taste.
One more thing: vlock is really useful when we work in ttys since we can leave a process running in the background and block the terminal AND THE ACCESS TO THE REST OF THE OTHER TERMINALS, INCLUDING 6, 7 AND 8 ONwards for a total control of the team.
Regards!
HAHAHAHAHAHA is that I like bright colors like that in the terminal, imagine ... 😀
Interesting about the fork 😉
I see that from a tty (xej: crtl + alt + f1) you log in as user or root and with vlock -a it blocks all the tty and you cannot even enter the session (ctrl + alt + f7) in that case it would be better than blocking the session.
Of course, if you run vlock from the graphical session it is innocuous
I honestly don't see any use for it
its effect is the same as the command «exit» since afterwards tb asks you to login, and even then anyone can change tty
what is your function?
I do not get it
I answer with what I read before I rolled it
vlock -a
this is really useful, I take note
Thank you
: )
I did not know it existed, just tipie vlock and it blocked, thanks !! 😀
Imagine a bit: I have my session open with my user, without root of course, I want to block a terminal that has root access, or for example I want to block a terminal that has an ssh to another machine, my friend wants to use the computer to navigate but I do not want to compromise that terminal with ssh or root, because I use vlock, the one that they do not see useful is that they do not have so much imagination, ha, the problems arise out of our interest our doubt, but if there is not such then we are truncated.
Excuse me, has someone used it in Ubuntu? .. I write vlock in the terminal and when I press [Enter] to unlock my terminal it gives me an error even if I write the root password correctly, open to edit any line for said configuration or something?
Thank you!
HAHA, YOU'RE PWNED !!!
Oh!! Ubuntu, Ubuntu ... xD
Did you know that the GENIUSES at Canonical decided long ago that with the advent of the SUDO tool, it is stupid for root to have its own password, since in this way they "eliminate" an attack vector against it?
In this way, all Ubuntus are released with the root account DISABLED, that is, without a password.
By doing basic math you will be able to realize that if VLOCK works with the root pass but the root pass OH, IT DOES NOT EXIST !!! then it is impossible for you to re-login to the XDD system
You have two options: either use another distribution that is handled differently or create a password for your root user as most distributions do that do not hide the base system from the user.
[Code]
$ sudo su
# passwd
[/ code [
Ready, now you can use VLOCK although of course, this goes against Ubuntu's design, something like adding repositories with updated software and kernels to Debian * cof *
xDDD When I used Ubuntu the first thing I did was open a terminal and put:
$ sudo passwd rootBecause if my user loaded me, how the hell was I going to manage my system? xDDD