Mozilla, Cloudflare and Facebook announced together the new TLS Delegated Credentials extension, who solves the problem with certificates by organizing access to a site through a content delivery network. Certificates issued by certification authorities have a long period of validity, which makes it difficult to organize access to the site through a third-party service, on whose behalf a secure connection must be established, since the transfer of the certificate from a site to an outside service creates additional security risks.
The new extension also can be useful for sites whose work is provided by a large distributed infrastructure with a large number of load balancers. The delegated credentials will help avoid storing copies of the private keys of the primary certificates on each content upload node.
With the classical approach, a successful attack on any of the servers involved in delivering HTTPS traffic will lead to the compromise of the entire certificate. In the case of private key transfer to content delivery networks, there are threats of data loss as a result of sabotage by staff, special service actions, or compromise of the CDN infrastructure.
If key loss goes undetected, key accessors will be able to silently enter site traffic (MITM) for a long time, as the validity period of certificates is calculated in months and years.
Cloudflare can use special key servers who work on the site owner's side to protect certificate keys, but work in this mode it generates noticeable delays in the delivery of traffic, reduces reliability due to the appearance of an additional link and requires the deployment of a sophisticated infrastructure.
The proposed TLS extension introduces an additional intermediate private key, cIts validity is limited to hours or several days (no more than 7 days). This key is generated on the basis of the certificate issued by the certification center and allows you to keep the private key of the original certificate from content delivery services secret by providing only a temporary certificate with a short lifespan.
To avoid access issues once the intermediate key has reached the end of its useful life, an automatic update technology is implemented on the source TLS server side.
To generate, you do not need to perform manual operations or run scripts: an authoritative server that needs a private key, before the expiration of the old key's useful life, accesses the site's source TLS server and generates an intermediate key for the next short time frame.
The browsers that support the credentials of the TLS extension they will perceive such derivative certificates as reliable.
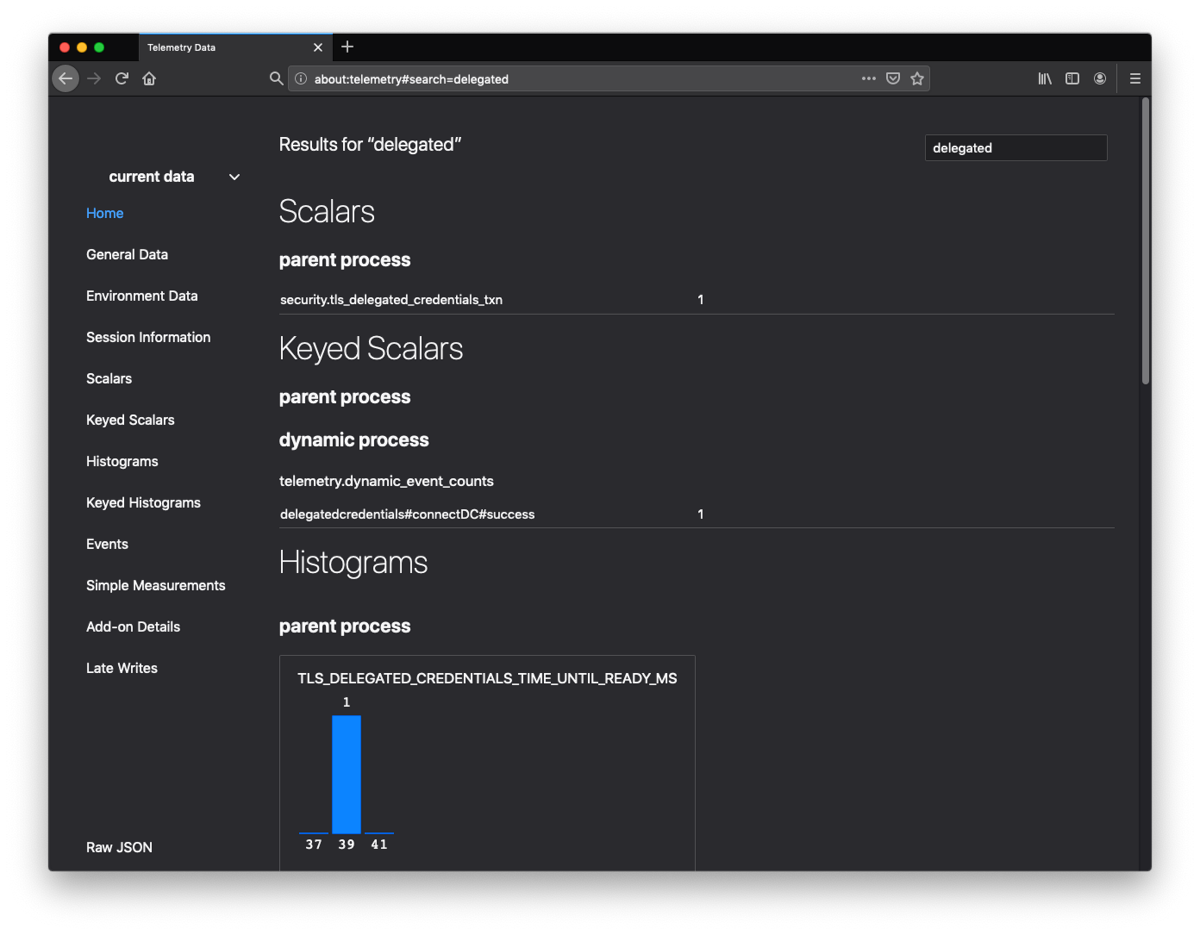
For example, support for the specified extension has already been added to nightly builds and beta versions of Firefox and can be activated in about:config changing settings "Security.tls.enable_delegated_credentials".
In mid-November, among a certain percentage of Firefox trial users, an experiment is also planned "TLS Delegated Credentials Experiment", in which a test request will be sent to the Cloudflare DC server to test the quality of the new TLS extension.
The TLS Delegated Credentials is also built into the Fizz library with the implementation of TLS 1.3.
The TLS Delegated Credentials specification was submitted to the IETF (Internet Engineering Task Force) committee, which is developing the protocols and architecture of the Internet, and is in the draft stage, claiming to be the Internet standard. The extension can only be used with TLS v1.3. To generate the intermediate keys, a TLS certificate must be obtained, which includes the special X.509 extension, which until now is only supported by the DigiCert certificate authority.
Si you want to know more about it, you can consult the following link.