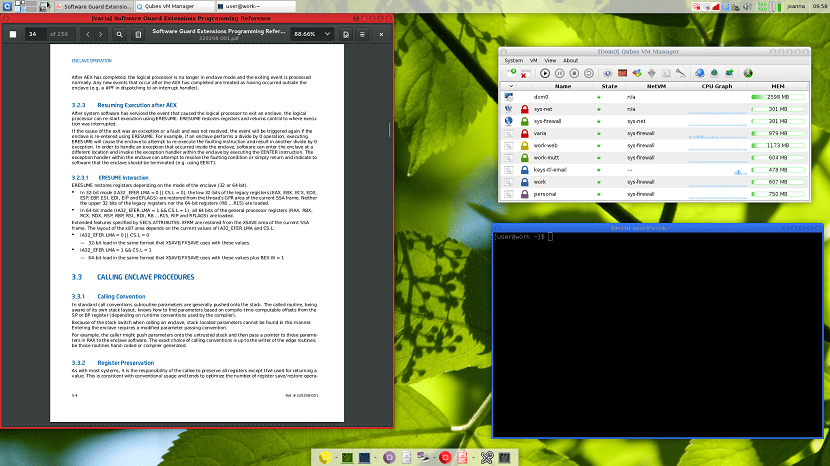
Qubes OS is an operating system focused on desktop security through isolation based on the Xen hypervisor. Qubes OS is an operating system totally free and open source.
Qubes takes an approach called security through compartmentalisation, which allows you to divide into isolated compartments safely called qubes. In other words, it runs each program separately in a totally isolated environment.
About Qubes OS
This is how Qubes OS offers the user greater security when working on the system, since if a program is compromised by an attacker, it will only obtain information about the compartment that it has managed to access.
Qubes achieves multiple virtual machines running on a Type 1 hypervisor they can be used safely as an embedded operating system.
For example, it puts all your application windows on the same desktop with specially colored borders that indicate the trust levels of their respective virtual machines.
Qubes handles different elements so that containers can interact with each other, andAmong the different types of virtual machines and elements we have: dom0, model virtual machines, model-based virtual machines, throwaway virtual machines and finally classic virtual machines.
Dom0 (AdminVM + GUIVM)
He is the driver. It is based on Fedora, controls the Xen hypervisor, and enables management of all virtual machines (VMs). You have access to the network and the peripherals present are very limited.
Virtual Machine Models (TemplateVM)
These son virtual machines with a GNU / Linux distribution. Accessed only on the command line to manage installed packages. The Qubes OS development team offers three models: Fedora, Fedora minimal and Debian. The community also offers others for Whonix, Ubuntu, and Arch Linux.
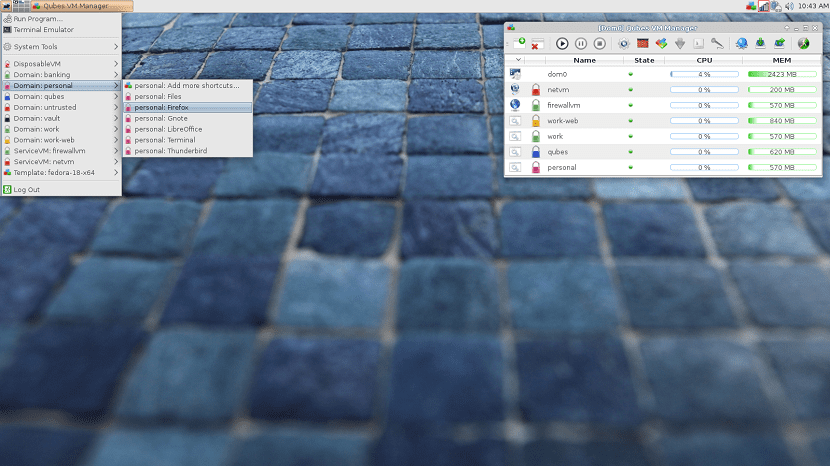
Model-Based Virtual Machines (AppVM)
They have some own directories / home, / usr / local and / rw / config. Any changes to files in other directories are done with a copy on the fly (copy on write) and is not sustainable: it will be destroyed when the virtual machine has been shut down or rebooted.
Disposable virtual machines
These are virtual machines that do not have their own directory, that is, when using this type of virtual machine, when making any modification, it is lost when the virtual machine is turned off.
Classic virtual machines
They are not based on a template, and you can install a GNU / Linux, BSD, or Windows distribution on it.
New version of Qubes OS
Some weeks ago Qubes OS developers released a new version of the system reaching this version Qubes 4.0 with various bug fixes and new modifications security to the system.
In Qubes OS 3.2, you could only use throwaway virtual machines with one model. AhNow it is possible to use a disposable virtual machine for each virtual machine based on a template.
Lmodel virtual machines no longer need a network interface, which results in a smaller attack surface. Updates do not pass the Qubes APIs.
Qubes OS version 4.0 allows you to use virtual machines to modify some characteristics of other virtual machines. This gives the possibility of having several families of admin type VMs, that is, admin-Net, admin-IO, admin-root, etc., each one with the possibility of modifying certain specific aspects of certain virtual machines.
By default, most virtual machines no longer use paravirtualization, thereby protecting containers from Meltdown and Spectrum failures.
If you want to know a little more about this new version, you can read the details in the release note of Qubes OS 4.0 in the following link.
Download Qubes OS
If you want to try this Qubes OS pYou can do it by downloading the system image from its official website and in its download section you will get it, you can do it in the following link
It is important to emphasize that Qubes OS can not only be installed as the main operating system, but also offers the possibility of being able to test it in its Live version.