Abaphandi kwiYunivesithi yasimahla yaseAmsterdam yaziwe kutshanje ndiyifumene ubuthathaka obutsha luhlobo olwandisiweyo lweSpecter-v2 sesichengeni kwi-Intel kunye ne-ARM processors.
Lo buthathaka obutsha, apho babhaptizwe njenge-BHI (Iinjection yeMbali yeSebe, CVE-2022-0001), bhb (Isithinteli seMbali yeSebe, CVE-2022-0002) kunye neSpecter-BHB (CVE-2022-23960), ibonakaliswe ngokuvumela ukujikelezwa kwe-eIBRS kunye neendlela zokukhusela ze-CSV2 ezongeziweyo kwiiprosesa.
Ubuthathaka buchazwa kwiimpawu ezahlukeneyo zomcimbi ofanayo, njengoko i-BHI luhlaselo oluchaphazela amanqanaba ahlukeneyo amalungelo, umzekelo, inkqubo yomsebenzisi kunye ne-kernel, ngelixa i-BHB ihlaselo kwinqanaba elifanayo lelungelo, umzekelo, i-eBPF JIT kunye ukhozo.
Malunga nokuba sesichengeni
Ngokwenyani, I-BHI luhlobo olwandisiweyo lohlaselo lweSpecter-v2, apho kudlula ukhuseleko olongezelelweyo (Intel eIBRS kunye neArm CSV2) kunye ne-orchestrate ukuvuza kwedatha, ukutshintshwa kwamaxabiso kwi-buffer kunye nembali yesebe yehlabathi (i-Branch History Buffer), esetyenziswa kwi-CPU yokuphucula ukuchaneka kokuqikelelwa kwesebe. ngokuthathela ingqalelo imbali yotshintsho oludlulileyo.
Ngexesha lokuhlaselwa ngokukhohlisa ngembali yotshintsho, iimeko zenzelwe uqikelelo olungachanekanga lwenguqu kunye nokwenziwa okuqikelelweyo yemiyalelo efunekayo, isiphumo sayo sifakwe kwi-cache.
Ngaphandle kokusebenzisa isithinteli sembali yoguqulelo endaweni yoguqulelo olujoliswe buffer, uhlaselo olutsha luyafana neSpecter-v2. Umsebenzi womhlaseli kukudala iimeko ezinjalo ukuba idilesi, xa usenza umsebenzi oqikelelwayo, kuthathwa kwindawo yedatha egqitywe.
Emva kokwenza ukutsiba okungathanga ngqo okucingelwayo, idilesi yokutsiba efundwe kwimemori ihlala kwi-cache, emva koko enye yeendlela zokumisela imixholo ye-cache ingasetyenziselwa ukuyifumana ngokusekwe kuhlalutyo lotshintsho kwixesha lokufikelela kwi-cache kunye nokungagcinwanga. idatha.
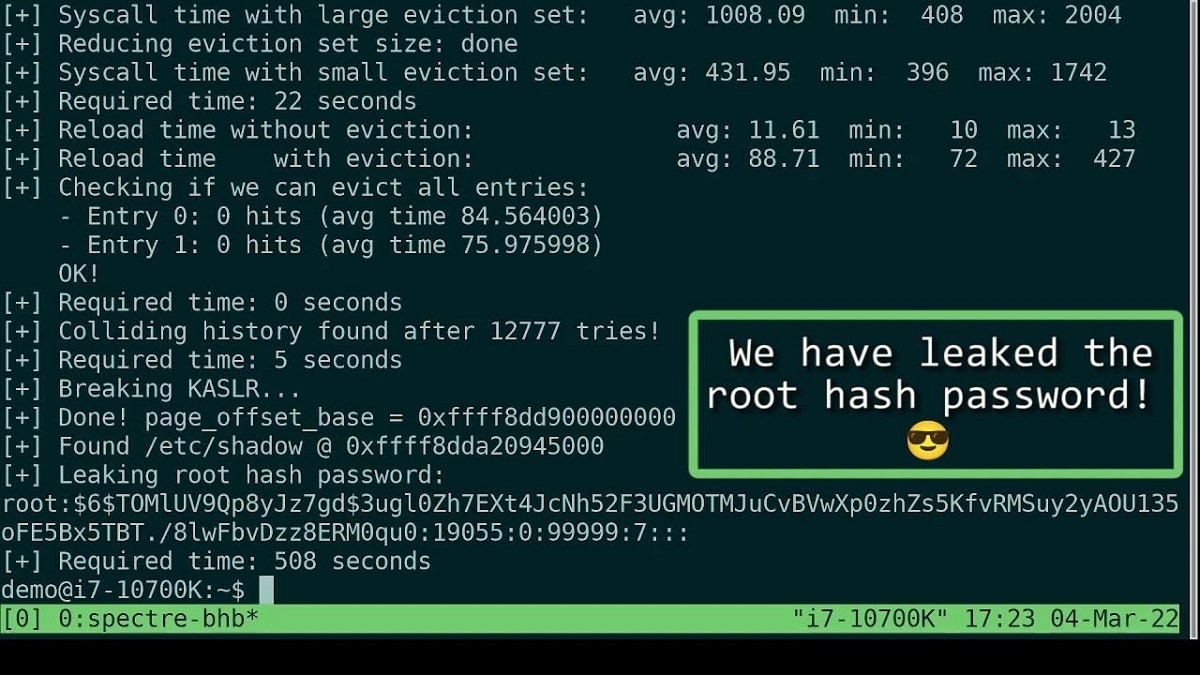
Abaphandi baye babonisa ukuxhaphaza okusebenzayo okuvumela indawo yomsebenzisi ukuba ikhuphe idatha engafanelekanga kwimemori ye-kernel.
Umzekelo, ibonisa indlela, usebenzisa i-exploit elungisiweyo, kunokwenzeka ukukhupha kwi-kernel buffers umtya onehashi yegama eligqithisiweyo lomsebenzisi wengcambu, elayishwe kwifayile /etc/shadow.
I-exploit ibonisa amandla okusebenzisa ubuthathaka ngaphakathi kwinqanaba elilodwa lelungelo (i-kernel-to-kernel attack) usebenzisa inkqubo ye-eBPF elayishwe ngumsebenzisi. Ithuba lokusebenzisa i-Specter gadgets ekhoyo kwikhowudi ye-kernel, izikripthi ezikhokelela ekuqhutyweni okuqikelelwayo kwemiyalelo, nazo azikhutshelwanga.
Ukuba sesichengeni ibonakala kwiiprosesa ezininzi ze-Intel zangoku, ngaphandle kweAtom yosapho lwabaqhubekekisi kunye nabaninzi bee-ARM abaqhubekekisi.
Ngokophando, ubuthathaka abubonakalisi kwiiprosesa ze-AMD. Ukucombulula le ngxaki, kuye kwacetywa iindlela ezininzi. isoftwe ukubhloka ukuba sesichengeni, enokuthi isetyenziswe phambi kokubonakala kokhuseleko lwehardware kwiimodeli zeCPU ezizayo.
Ukuvala uhlaselo ngokusebenzisa inkqubo ephantsi ye-eBPF, sKuyacetyiswa ukukhubaza ngokungagqibekanga ukukwazi ukulayisha iinkqubo ze-eBPF ngabasebenzisi abangenalungelo ngokubhala i-1 kwifayile "/proc/sys/kernel/unprivileged_bpf_disabled" okanye ngokusebenzisa umyalelo "sysctl -w kernel .unprivileged_bpf_disabled=1".
Ukuvala uhlaselo ngokusebenzisa izixhobo, kucetyiswa ukuba usebenzise umyalelo we-LFENCE kumacandelo ekhowudi enokuthi ikhokelele kumiliselo oluqikelelwayo. Kuyaphawuleka ukuba uqwalaselo olungagqibekanga lonikezelo oluninzi lweLinux sele lunamanyathelo okhuseleko ayimfuneko ngokwaneleyo ukuvimba uhlaselo lwe-eBPF oluboniswe ngabaphandi.
Iingcebiso ze-Intel zokukhubaza ukufikelela okungekho sikweni kwi-eBPF zikwasebenza ngokungagqibekanga ukuqala ngeLinux kernel 5.16 kwaye iya kuthunyelwa kumasebe angaphambili.
Okokugqibela, ukuba unomdla wokwazi ngakumbi ngayo, ungajongana neenkcukacha kwi ukulandela ikhonkco.