Sometimes we program a script in Bash and we want the code of this to be NOT visible, that is, not to be plain text. When we talk about hiding code the correct term is obfuscate, in my case I wanted to obfuscate the code a script that I did some time ago, the utility I found for this is called: shc
shc It allows us to obfuscate code, here are the steps to use it:
1. First we must download it
2. Once we have downloaded it, we right click on the compressed file and select the option that says «Extract here" or something similar. This will make us see a folder called shc-3.8.9, here I show you a screenshot of its content
3. OK, let's say the folder is at /home/usuario/Downloads/shc-3.8.9 Well, we open a terminal and go to that route (cd "/home/usuario/Downloads/shc-3.8.9"), and the installation begins here.
4. In the terminal being located (as I already told you) in the folder shc-3.8.9, in order to install this application we need to make a symbolic link of the file shc-3.8.9.c a shc.c so we execute the following:
ln -s shc-3.8.9.c shc.c
4. Once the link is made, we execute make install with root permissions (we will use sudo):
sudo make install
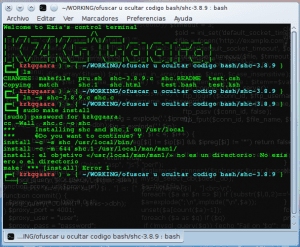
4. It will ask us for our password and it will wait a moment, it will be waiting for us to press the key [AND] and press [enter], that is, that we confirm that we do want to install the software. Once this is done it will install without problems. I leave you a screenshot of the entire preparation and installation process:
sudo make install es NECESSARY have the packages installed: gcc y make5. Done, this is it for the installation 😀
When we have it installed, we just need to learn how to use it. Suppose we have a script in our home called script.sh and that its content is as follows:
#!/bin/bash
echo "Script de prueba para DesdeLinux.net"
exit
When executing this script it will obviously show us the message in the terminal: «Test script for DesdeLinux.net" or not? … But, now we are going to obfuscate that code.
In a terminal we put the following and press [enter]:
shc -v -f $HOME/script.sh
And bingo !! ready 😀
This created us two new files together with our script, now we have script.sh.x y script.sh.xc
script.sh.x - » This is our obfuscated bash script, this when we execute it will do exactly the same as the first one we created, the difference between these is that the first one if we opened it with a text editor (nano, kate, gedit, etc) we could see clearly its content, while if we open to script.sh.x we will clearly see that we do not see anything ... LOL !!!, that is, the code is 'encrypted' 🙂
script.sh.xc - » This is our script but in C language ... we can delete this without worry because we don't really need it, well, at least I wouldn't need it at all 🙂
There's not much else to add actually on the technical side, just clarify that as far as I know with this (hiding or obfuscating bash script code) it is not violating licenses or something like that. I clarify this because a few months ago on Facebook when I mentioned that I had learned to obfuscate bash code, some users alerted me that this was violating licenses or something like that ... well, as far as I understand, licenses are not violated with this 😉
Nothing more to add, any doubt or question, complaint or suggestion let me know.
regards
It is not that licenses are violated, it is that it stops being free software ...
Yes of course. The point is that there are certain personal scripts of mine that I do not want others to see, for example because one of these script has a password in plain text of my local MySQL, or something similar.
NO! Don't save your passwords in scripts!
http://technosophos.com/content/dont-script-your-password-add-simple-prompts-shell-scripts
Actually I keep my passwords 'hidden' using SHA (https://blog.desdelinux.net/como-saber-la-suma-md5-o-sha-de-una-palabra-oracion-o-archivo/), then in the script I keep the password hash and what I do is compare the password that the user enters (I save it with read), I get the SHA sum and compare both at the end 🙂
Anyway, thank you very much for the link, I'm already reviewing it 😀
regards
Exact! A shell prompt asking for the password is a good alternative.
Cheers! Paul.
But it does not provide an automatic and unattended execution as it does the other way. 🙂
Putting passwords and other access or compromising data in the script is a big mistake. This information has to be saved in another file, with its proper permissions, so you will not have to obfuscate your bash script. Easy huh?
The problem with having the data (login variables, confs, etc) in another file is that then the 'system' or 'application' needs 2 files to function, whereas if I store as 'secure' as possible everything in one single file, well I would only need that ... a single file.
It is good practice to separate the application from the data.
Or rather it is a terrible practice to hardcode the data!
http://es.wikipedia.org/wiki/Hard_code
It has nothing to do with security putting code and data in the same file. And even more, quite the opposite if you have your passwords there !!
The cost of reading sensitive information from another file is negligible next to the processor cost needed to "unobtain" your code.
On the other hand, you are throwing away a whole paradigm of modular development, betting on a monolithic model that, more than proven, there are more problems than solutions.
And also that if you use permissions that are necessarily going to involve other groups / users, you will still need an initial password to execute the first script.
@KZKG the comment above is in response to your comment
@morpheus: it is absolutely relative to the particular need.
But there is free software compiled in binary (which is more than obfuscate). The fact that it is free implies that it also has the source, but it has nothing to do with obfuscating (or compiling, which is essential if I want to run a C program, for example)
In the case of compiled free software, it is a question of the requirement of the language that is used (if you program in C, you have to compile for your application to work). And the same, always, if it really is Free Software, the source code will be available.
humm I denote a certain degree of apathy to share code lol to see how many end up beginning to "obfuscate their codes" to make us more dependent on their solutions ...
I'm not saying that code should be obfuscated or not ... I give the tools, each one to use them according to their needs.
Obfuscate code on this page?
I think it is a good idea to distance readers, since I consider that many of the people who visit this blog are followers of free software, and therefore we do not share the practice of obfuscating code.
You obviously didn't read the reason KZKG argues and why it explains its need to obfuscate its script.
Thanks KZKG for sharing your find!
And so viruses start to circulate in Linux ...
Personally I would NEVER use any obfuscated scripts. Not only because of the security risks involved, but because if your script is too precious to you to share then better put it in the * ulo; I can surely find someone who does want to share their knowledge.
Would you ever use an obfuscated script ?, Well, VERY good for you, I would NEVER use an obfuscated script ... the detail is that, I have NEVER shared an obfuscated script, far from it, and there dear friend is where the mistake is present presente
Whenever I do something in Bash I share it without weighing or bothering me, which I have already done in many articles here 😀
Welcome to the blog, a pleasure to read you 😉
Gabriel, KZKG ^ Gaara is already sharing knowledge, he is not creating any linux package with obfuscated scripts which if it could be a license violation, it only reveals applications that one can use or not for their own use, it is not necessary be rude, as for viruses in linux is not that simple, here is a good article about it https://blog.desdelinux.net/virus-en-gnulinux-realidad-o-mito/.
KZKG ^ Gaara I would like you to write a post about encfs and cryptography using images, it is a topic that I really like.
Cheers !!!
Thank you
Actually, it is not that I have enough knowledge about encfs and cryptography, at least I do not feel confident enough to make a post and assume the doubts that users may have 😀
In this topic it is not that I am an advanced user ...
The most I've done is using GPG to encrypt files, and as for images, the most I've done is 'insert' or hide a file inside an image, making it obvious that when the image is opened with an image viewer, everything is shown correctly, is this what you mean?
Once again, thank you very much for your comment 🙂
If I remember correctly, there are obfuscated C championships, but it is not worth using an "obfuscator" but they have to obfuscate their sources bareback.
As for shc and your script's with passwords… very bad way to work!
Interesting article, as always.
Yes, more than one have already told me LOL !!
Thank you for your comment 🙂
Basically, if you share the application without sharing the visible script you would be violating the GPL, which requires that anything generated with a GPL application be GPL. That's why SHC generates the C, because that's the code that you can share.
regards
I agree with the comments of other readers: not only is it not a good practice to store data and script all together but it is also not conducive to the development of free software.
A hug! Paul.
Hello Pablo 🙂
I have some other obfuscated script that works internally on my laptop, I obfuscate it because I simply do not want that if someone for some reason managed to copy my script to another computer, I simply do not want them to be able to see what it contains, it is a 'security measure 'I take.
However, here in DesdeLinux I make public everything or almost everything I program in Bash that might be interesting.
In short, it is not that I am now a detractor of the SWL for obfuscating a personal script, for doing this for personal purposes 😀
Greetings friend
Good information. Apart from the controversies that are being generated in the comments, it seems to me information to continue investigating a little more.
I think that the author at no point in the article tells us if it is good or bad done or if we should or should not do it, he simply tells us the tool with which it can be done in case it is of benefit to someone.
A greeting.
codelab
In Linuxeros blogs everything is controversial, haha it has always been like that.
@ F3niX I'm going to cut a screenshot with your comment to put it every time someone makes some stupid mention of the subject.
Note: let's see when I find you through the irc and Chakra forums 😉
EXACT!!
I simply show / teach / explain something new that I learned, it is up to you to use this knowledge or not, I do not force you far from it.
As far as I know, sharing knowledge is a good thing, right? 0_oU
Thank you for your comment, it is good to know that there are more than one or two who understand the true purpose of this article.
There you put me in a tight spot xD, a few weeks ago I have been preparing a post that was going to be titled «Installation and testing of Crux» and despite the fact that the installation was carried out successfully, I am a normal user and I don't know if I will be able to cope with the doubts from third parties, the intention is that it serves as an instrument of discussion about the virtues and defects of this distro and the possible solutions to problems that may arise helping us among all users and readers. When I finish it and send it for review, you (Administrators) will decide. As for the cryptography issue in images it was the same, thanks KZKG ^ Gaara for answering.
Regards!!!
Ok with pleasure, I'll make a post about that 😉
excellent tuto bro I found it very useful: 3
for those who want to install it in manjaro linux and derivatives of archlinux the package is in aur with the name: shc
regards
Excuse me, friend, I had a small script that converted CAPITAL LETTERS TO lowercase letters that were in the clipboard
the script works normal when not obfuscated
#! / Bin / bash
xclip -o> R1.txt
cat R1.txt | tr [: upper:] [: lower:]
threw out ""
rm R1.txt
but when i want to run the obfuscated script
tells me
./M2m.sh: Operation not permitted
Completed (killed)
Please help
Do you have xclip installed?
It should be noted that it is actually a bash compiler, as there are .bat compilers or .php.
I do not know if the code that produces is encrypted and obfuscated and does not withstand a decompiler, it would be necessary to try, since it is not my field I do not say yes or no, but what I see that it does is compile a bash, in the .c it is You can see the code, which, within the obfuscated, I see that it is in lines that look like an exploit shell, I do not know if they are really obfuscated, since, no password is requested or a I do not know, master.config where a previous keyword.
friends it happens that when I obfuscate my script he creates the new script with ex ending, I execute it and there is even perfect. But when I take it to another computer with linuz it does not run, it already has all the permissions, I create a launcher and tell it that it is a terminal application, but it does not work, please wait for a prompt response
Did you compile it and are you running it on a system with the same architecture? That is, it will give you an error if you compiled it to obfuscate it on a 32-bit system, and then you try to run it on a 64-bit system, or vice versa. You understand?
No, but I already provided formatting the same computer, with the same operating system and it does not run, it does not even send an error.
I call it by console like this: sudo /home/operations/script.x and I get this error
/home/operaciones/script.x: e } 8- q , K
a whole case
Try to run it WITHOUT compiling to see if it is an error in the code
In order for you to run the obfuscated script on other computers you have to compile it with the option «-r Relax security. Make a redistributable binary ', otherwise it will only run on the machine where the script was obfuscated with SHC.
Example:
shc -r -f script.sh
Hello, I have a query, the shc can be installed in any type of Linux distribution ?, for example red hat, how would the installation be for this one?
Thank you!
Hello everyone, your comments have helped me a lot, but I have the following problem, when obfuscation does not work for me in the same system but with different architecture, that is, if I do it in 32 bits it cannot run in 64 bits. Does anyone know if it can really be run on different architectures (32 and 64 bit)?